With cyber threats on the rise, securing your WordPress site is essential. WordPress powers over 40% of global websites, making it a prime target for cybercriminals: One study found that 61% of small and medium businesses (SMBs) in the US and UK were hit by a cyberattack in the past year. Fortunately, there are several steps you can take to reduce your website’s risk of falling victim to these kinds of attacks.
These methods, designed to strengthen your website’s defences, are also known as ‘hardening’. By taking a comprehensive security approach, you can reduce breach risks and keep your digital presence secure. This guide outlines WordPress hardening steps for a strong security strategy.
What is WordPress security?
WordPress security is more than just reacting to cyber threats. The main goal is to defend against attacks and block unauthorised access, but a truly comprehensive security posture must include a proactive approach. With the right measures, you can diminish the risk of attacks by identifying and fortifying potential vulnerabilities ahead of time.
Security strategies should include proactive measures to prevent attacks, as well as reactive protocols to block or mitigate attacks in real time. It’s important to recognise that breaches may occur despite the best-laid plans. With this in mind, your security plans should ensure your resilience in the face of a successful attack by including a backup and recovery strategy .
Guiding concepts for your security strategy
Adopting a multi-layered security approach combines prevention, detection, and response for a strong defence system.
The ‘defence in depth’ concept promotes multiple security layers to prevent breaches. Containment minimises damage in case of a compromise. The Principle of Least Privilege (POLP) advocates for minimal user access levels to mitigate unauthorised access risks.
Limiting entry points and using trusted sources for plugin downloads will enhance site security. Committing to regular security audits, updates, and disaster preparedness is necessary, illustrating that security management is ongoing, and not a one-off task.
Basic steps to secure your site
Securing a WordPress site involves basic steps, starting with your behaviour and adoption of best practices. Using strong passwords, with help from a password manager, is fundamental. Login security enhancements are vital – e.g. limiting login attempts will counter brute force attacks.
Adopting SSL certificates is critical for secure communications for your customers, and choosing a hosting service that prioritises WordPress security features adds an extra layer of defence. Regular updates to the WordPress core, themes, and plugins goes a very long way towards security of your site.
These crucial first steps form the foundational layer to comprehensive security strategy. Advanced strategies, discussed later, position your site defensively sophisticated threats.
Looking deeper: Where do vulnerabilities come from?
Improved WordPress security will follow from a better understanding of what sort of WordPress vulnerabilities are out there, and you’ll be better equipped to protect your sites. Let’s take a look at some of the vulnerabilities that can impact WordPress sites.
Your computers and devices
As an admin, how you access your WordPress sites (via the internet) and the devices you use, influence the security of these sites. Malware and viruses on personal computers can steal vital credentials like FTP, WP-admin logins, & WP admin sessions. This poses a massive threat to your sites.
It’s critical to ensure your local environment is secure – regular antivirus updates and best practices for device security are essential. Always fully log out of secure programs or websites when finished, and use a good Password Manager to help use unique, strong passwords. Neglecting personal device security jeopardises data and risks cross-contamination to the WordPress sites you manage.
WordPress
While WordPress has strong security measures, it’s not impervious to threats.
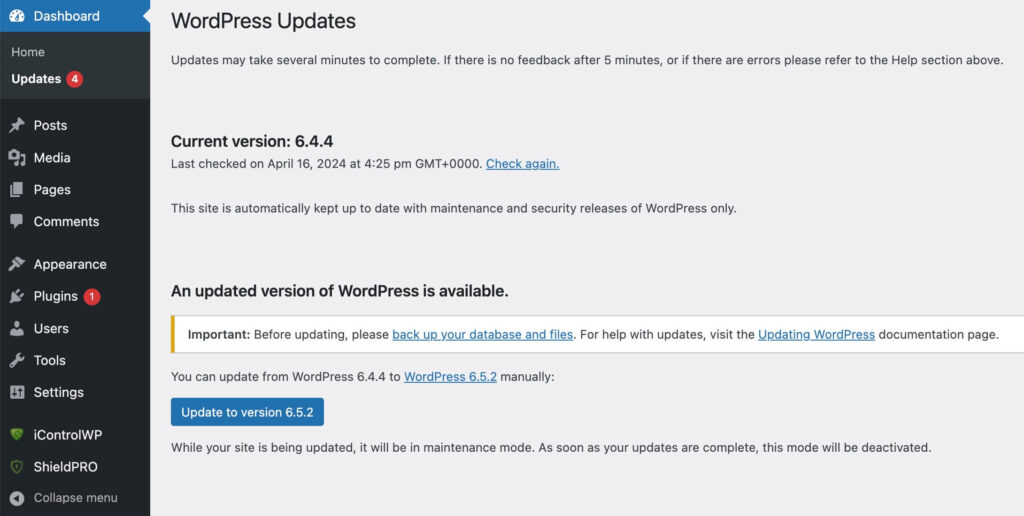
Vulnerabilities can come from outdated core software, plugins, or themes. Regularly updating WordPress and its components is crucial. Since version 3.7, WordPress has enabled automatic updates to patch known vulnerabilities. Outdated installations are prime targets for exploitation, as old vulnerabilities are public knowledge.
Web servers
The web server hosting your WordPress site is another potential source of vulnerabilities. Using up-to-date, secure, and stable server software—or a hosting provider that guarantees this—is one of the most critical decisions you’ll make.
Vulnerabilities can stem from misconfigurations, outdated software, or other hosting tenants compromising security on a shared server. Therefore, the choice of the web server or host is critical. Opt for hosts prioritising security and offering server-level features like firewalls to best safeguard your site.
Networks
Insecure networks will expose passwords and sensitive information. It’s crucial to address network-level vulnerabilities, such as insecure Wi-Fi and man-in-the-middle attacks. Secure network practices, particularly for remote WordPress site management, is vital. This involves using VPNs where appropriate and TLS/SSL encryption to protect data in-transit.
Hardening your WordPress site with the help of a plugin
With numerous avenues for vulnerabilities that leave your WordPress site open to attack, addressing each threat individually is burdensome. The diversity and complexity of these threats require more time and expertise than most site owners can afford. Utilising a dedicated plugin or service for site hardening is often a hugely practical solution.
WordPress security plugins streamline the hardening process, addressing vulnerabilities timely and effectively. For those who prefer manual intervention, the following section will outline key elements of a WordPress site that require attention, based on their significance and exploitation frequency.
Using a security plugin will save time and effort that can be put to focus on other business-critical tasks, and also avoid complex coding that may even introduce further vulnerabilities. A good security plugin invests resources into identifying and mitigating threats for you, covering all major high-priority areas. These plugins enhance security in areas often overlooked by website owners and developers
When choosing a security plugin, key considerations should include:
- Update frequency.
- Ease of use.
- Customer support quality.
- The plugin’s reputation.
- Proven effectiveness against a wide spectrum of threats.
Website hardening with Shield Security Pro
Shield Security PRO is a comprehensive solution for WordPress sites, offering a wide range of security features, from malware scanning and removal, to bot detection and blocking, firewalls, and SPAM blocking.
Shield Security PRO stands out with its AI-powered deep malware scans, customizable automatic updates, and web-application firewall, delivering a multi-layered defence-in-depth. Its easy configuration makes securing a WordPress site clear and understandable for users of any skill level.
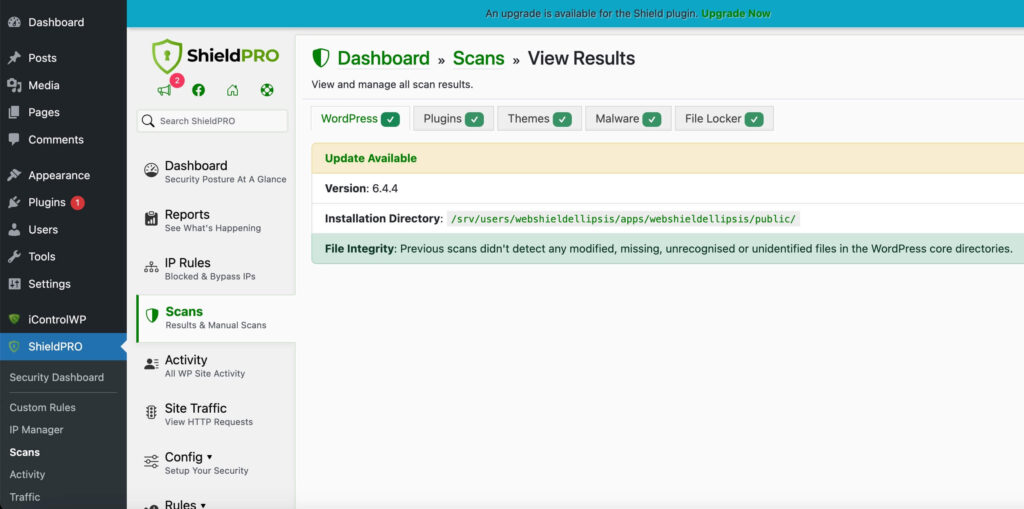
Shield Security PRO offers manual and automatic options for responding to threats. For example, you can set it to simply alert you to changes in your site’s files or it can automatically replace the damaged file with a clean version of the original WordPress file, saving you time with trivial fixes.
This proactive stance is complemented by positive feedback from a broad user base, as evidenced by excellent customer reviews and testimonials.
Manually securing important elements of your WordPress site
Plugins like Shield Security PRO are crucial for securing your WordPress site, but manual actions can further enhance security. These measures strengthen your site’s defence, boosting its resilience.
File permissions
Setting file permissions is crucial for WordPress security. They control file access, playing a critical role in site protection, especially in shared hosting.
- For most files, a permission setting of 644 is recommended. This allows you, the file owner, to read and write, while others can only read.
- Directories should be set to 755, enabling the directory owner to read, write, and execute, with others limited to reading and executing.
- The wp-config.php file, containing sensitive information, should ideally have permissions set to 600 or 640, restricting access only to you or your group.
Checking and modifying file permissions: Step-by-step
- Via SFTP:
- Connect to the website using the FTP client with SFTP login details provided by your hosting provider.
- Navigate to the WordPress root directory (often named public_html, www, or named after the site).
- Right-click on a file or directory to check its permissions.
- Select ‘File Permissions’. A dialog box will appear showing the current permissions. The permissions will appear as numeric values (e.g., 644 or 755) and checkboxes for read (r), write (w), and execute (x) permissions.
- To change permissions, either modify the numeric value or check/uncheck the corresponding boxes.
- Using a file manager in cPanel:
- Find and open File Manager (most hosting providers offer cPanel or a similar control panel that includes a File Manager tool).
- Navigate to the WordPress root directory.
- Right-click on a file or directory and select Change Permissions or Properties.
- Adjust the permissions using the interface provided, then save the changes.
- Using SSH (Secure Shell):
- For command-line use. Connect to the server via SSH using a terminal or SSH client.
- Navigate to your WordPress directory using cd (change directory) commands.
- To view permissions, use the ls -l command, which lists files and their permissions.
- To change permissions, use the chmod command followed by the permissions value and the file or directory name.
You can set permissions to allow only the admin to edit most files, while giving the web server write access to necessary files only. The admin alone should be able to modify wp-admin, wp-includes, and wp-plugins directories, while both the admin and the web server can write to wp-content.
Database security
Database security is crucial for protecting your site’s data and user information. Enforcing strong passwords and user privileges is essential. Implementing containment (separating databases with distinct access levels) ensures a breach in one doesn’t compromise all. This is useful for managing multiple blogs on a single server, protecting data integrity, and minimising widespread data exposure in any attack.
Disable XML-RPC
XML-RPC allows remote communication with your WordPress site but can be a security liability, exposing your site to brute-force login attacks. You can disable it manually, or Shield Security PRO offers a straightforward option for easily managing XML-RPC.
Consider whether or not disabling XML-RPC fits your site’s needs, as it may impact useful functionality. For detailed information, refer to our guide on disabling XML-RPC.
Preparing for attacks and disaster recovery planning
Preparing for cyber attacks and having a disaster recovery plan are essential components of a WordPress security strategy. A well-thought-out plan facilitates a swift recovery by minimising the damage to your site and your reputation.
Evaluate your current security measures to identify vulnerabilities in your WordPress site and hosting environment. Develop an actionable, step-by-step protocol for responding to security incidents. Include clear measures for immediate containment, threat elimination, and restoration of normal operations. Quick action is key to mitigating the breach impact.
Ensure you have a backup of your site to restore it if attacked. Regular, secure backups are crucial for web security. If something goes wrong, you can restore to the last clean version and easily reset your site to a safe state.
Lastly, stay updated on cybersecurity news and developments by following cybersecurity blogs and experts to be aware of emerging threats. This helps you proactively protect your website.
Harden your WordPress site with Shield Security PRO for complete site security
A comprehensive security strategy goes beyond eliminating risks – it includes reducing threats and preparing for disaster recovery. This article explores crucial steps and best practices for securing your WordPress site, emphasising proactive measures and continuous education on cybersecurity threats.
Manual hardening methods are available, but they require technical expertise, are time-consuming, and less effective. Shield Security PRO offers a solution with features like malware scanning, automated backups, advanced firewalls, and incident response tools for comprehensive WordPress security.For those seeking a reliable and robust security system for their WordPress site, Shield Security PRO is the ideal solution. Its focus on proactive defence and disaster recovery positions it as a valuable tool in keeping your website safe. Harness the power of Shield Security PRO today and fortify your WordPress site against digital threats.